The CEO's Guide to Preventing SaaS Trial Abuse and Fake Signups
SaaS trial abuse costs the industry trillions in hidden losses. This playbook provides a strategic framework to identify 'invisible churn' and deploy a multi-layered defense to protect your growth metrics.
Your SaaS is likely leaking revenue through a hole the size of the global economy. By 2025, fake registrations and subscription fraud are expected to cost the industry a staggering $4.8 Trillion in annual revenue loss.
This isn't just about losing a few dollars on server costs. It is about the data you use to make board-level decisions being fundamentally poisoned by users who do not exist.
Every time a bad lead hits your database, you are effectively burning cash. The average marketing and infrastructure cost for a single fake registration is $408 per lead.
We call this 'invisible churn'. The user didn't lose interest or find a better tool; the user was never real in the first place.
If you are seeing high signup volume but stagnant MRR growth, you don't have a conversion problem. You have an identity problem that needs a CEO-level fix.
The Bottom Line On Trial Protection
Stopping trial abuse is about increasing the cost for bad actors without slowing down your actual customers. You need a defense that operates in milliseconds at the front door.
- Audit your data: Identify how many 'users' have zero activity after the first 24 hours.
- Verify the source: Block disposable email domains that accounts use to bypass limits.
- Score the risk: Use real-time IP and device intelligence to flag professional abusers.
- Protect resources: Prevent trial-farmers from draining expensive AI or GPU compute credits.
According to the LexisNexis Fraud Multiplier Report, every dollar lost to fraud costs companies significantly more in recovery and operational overhead. Addressing this at the registration point can cut registration fraud by 94% and protect your margins.
Why Single-Layer Defense Is Failing Your Metrics
Most legacy defenses rely on reCAPTCHA or basic IP blacklisting to stop bots. Unfortunately, modern abusers use residential proxies and anti-captcha services to look exactly like your target audience.
Over 52% of all digital platform fraud attempts now originate at the signup stage. This isn't just hobbyist users trying to get a second free week; it is a professionalized industry.
Professional abusers create accounts at scale to farm credits, scrape your data, or resell access. Single-layer defenses are effectively transparent to these automated scripts and persistent humans.
If your SaaS offers high-value resources like AI generation or deep-data exports, you are a prime target. The drain on GPU and compute resources can quickly turn a profitable month into an infrastructure nightmare.
Pitfall: Relying solely on 'email confirmation links' is useless against disposable email services. These temporary inboxes allow bots to verify accounts automatically in seconds.
How To Identify The Signs Of 'Ghost' Users
Identifying 'ghost' users requires looking at patterns, not just individual actions. You need to look for anomalies in how and when users enter your ecosystem.
Start by monitoring 'velocity spikes' in your server logs. If you see multiple signups from the same IP range in under 60 seconds, you are likely under a scripted attack.
15-30% typical fake registration rate for SaaS companies without protection.
Next, look at engagement metrics within the first day. Users who sign up and perform zero actions within 24 hours are rarely 'distracted'—they are usually automated entries or temporary accounts.
- If an email domain is found on a disposable list, then reject the registration immediately.
- If the user's IP is associated with a known data center or proxy, then trigger a high-friction verification step.
- If multiple accounts share a single device fingerprint, then flag the accounts for manual review.
- If a signup originates from a region you don't serve with a high-risk IP, then block the session.
Data shows that 33% of freemium accounts in 2025 use disposable email domains (DEAs) to hide their identity. By identifying these early, you stop the 'invisible churn' before it hits your CRM.
The Multi-Layered Defense Framework
A resilient defense is built in layers, ensuring that if a bot bypasses one check, it hits another. This creates a cumulative 'friction cost' that makes your platform too expensive to attack.
Imagine a Series B startup scaling an AI video editor. They saw signups triple in a month, but GPU costs ballooned by 400% while MRR stayed flat because thousands of bot accounts were farming credits.
Layer 1 starts with real-time email validation. You must block temporary domains at the moment of entry using a service like IsFakeMail to ensure the lead is reachable.
Layer 2 involves IP reputation checking. You need to know if the user is coming from a Starbucks Wi-Fi or a server farm in a foreign country designed to mask their identity.
Layer 3 uses device fingerprinting to track the 'hardware signature' of the visitor. This is crucial because even if an abuser changes their IP and email, their browser and hardware profile stay the same.
Layer 4 is progressive feature unlocking. For high-risk signups, don't give them the 'Pro' features immediately; wait until they complete a profile or verify a phone number.
This multi-layered approach keeps the door wide open for your real customers while slamming it shut on automated scripts. Consistency across these layers is what preserves your data integrity.
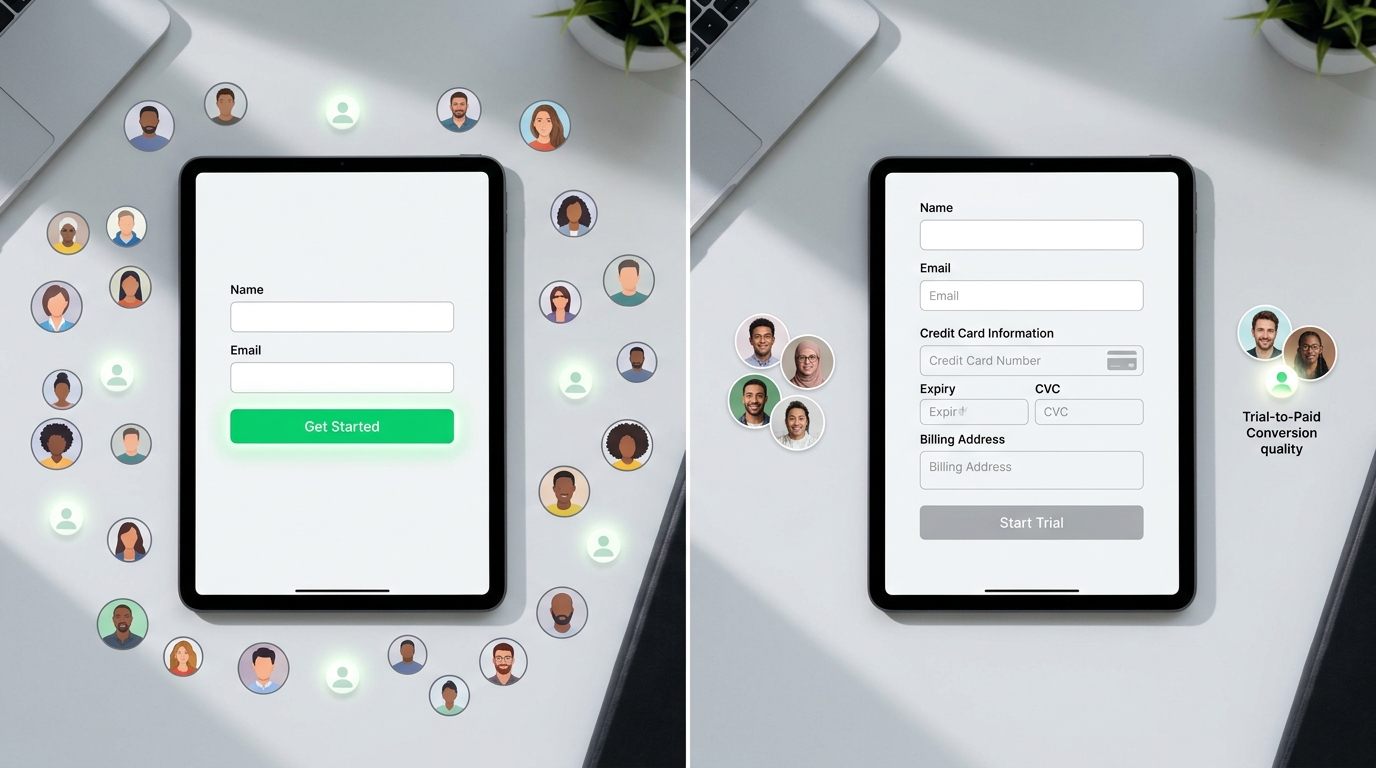
The Friction Paradox: To Require Credit Cards Or Not?
One of the hardest decisions for a SaaS CEO is whether to ask for a credit card upfront. This single field can be the difference between a clean user base and a marketing ghost town.
Requiring a credit card can drop your signup volume by 30-60%. For many growth-stage companies, that is a terrifying prospect that limits the top-of-funnel reach.
However, the users who do sign up are significantly higher quality. Trial-to-paid conversion rates are often 5x to 10x higher when payment info is collected at the start.
There is a middle ground: the hybrid model. You can offer a frictionless entry for basic features but require a card for high-compute or 'Pro' testing.
This protects your most expensive resources while allowing the marketing team to keep their 'low friction' signup numbers. It forces the abuser to spend money to steal, which usually ends the attack immediately.
Top Tools For SaaS Trial Protection
Building a defense stack requires specialized tools that handle the 'dirty work' of identity verification in real-time. Here are the core components of a modern anti-abuse engine.
IsFakeMail
This is a real-time disposable email detection service that helps you block temporary addresses during registration. It uses a massive database of over 187,000 domains to ensure signups use permanent, reachable emails.
Sensfrx
Sensfrx provides real-time risk scoring by analyzing user behavior and signup patterns. It is designed to stop account takeovers and registration fraud before they affect your bottom line.
Stytch
For identifying repeat offenders across different accounts, Stytch Device Fingerprinting is the gold standard. It creates a unique identifier for every device, making it nearly impossible for one person to create dozens of 'new' trials.
APIVoid
APIVoid Email Intelligence provides deep data on IP and email reputation. It is a great choice for engineering teams that need a raw data feed to build custom internal risk logic.
OnSefy
OnSefy uses AI-powered validation to detect high-risk signups that typical rules-based systems might miss. It analyzes the context of the signup to provide a 'fraud probability' score instantly.
The 90-Day Roadmap To Fraud Reduction
You don't have to fix everything today. A phased approach allows you to secure the system while your engineering team maintains its product roadmap momentum.
In the first 30 days, focus on the audit. Use your CRM and server logs to establish a baseline of fake vs. real users and identify your biggest vulnerabilities.
Days 31 to 60 are for implementation. Add real-time email validation to your signup form to block DEAs and check MX records to ensure the domain can actually receive mail.
# Example check for a disposable domain using IsFakeMail API
curl https://api.isfakemail.com/v1/check/example@temp-mail.com
# Result: { "disposable": true, "suggestion": "Use a personal or work email" }
In the final 30 days, deploy device fingerprinting. This will allow you to see the 'web of accounts' often created by a single abuser using different email addresses.
Rule: Never block users based on a single data point; always use a weighted score from at least three different signals before denying access.
By day 90, your trial-to-paid metrics will likely look very different. You will see fewer signups overall, but your conversion percentages will skyrocket as the 'noise' of fake accounts disappears.
Comparing Prevention Strategies By ROI
| Strategy | Effectiveness | Implementation Effort | ROI Potential |
|---|---|---|---|
| Email Validation | High | Low | Very High |
| IP Reputation | Medium | Low | High |
| Device Fingerprinting | Very High | Medium | Very High |
| Credit Card Upfront | Very High | Low | Variable |
| Progressive Unlocking | Medium | High | Medium |
Each of these strategies serves a different purpose in your defense. Real-time email validation offers the fastest path to cleaning your lead database with the least amount of engineering overhead.
Common Questions On SaaS Trial Abuse
How much friction is too much for a trial?
If your product has a high time-to-value, minimize friction at the start. Use 'invisible' checks like email domain validation and IP reputation so real users never even know a security check is happening.
Will blocking disposable emails hurt my conversion rate?
It will lower your total signup count, but it will increase your lead quality. Users who use disposable emails rarely convert to paid plans, so you are only losing 'junk' data that costs you money.
Can I just use reCAPTCHA v3?
While v3 is better than the older 'click the bus' versions, professional abusers bypass it easily. It should be one small part of your defense, not the entire strategy for protecting premium resources.
How often should I audit my signup logs?
A monthly audit is sufficient for most SaaS companies. However, if you see a sudden spike in infrastructure costs or a dip in engagement, you should run a verification check immediately.
Protecting Your Product's Future
Free trials are your most powerful growth tool, but left unguarded, they become your biggest liability. Every fake account in your system is a drain on your focus, your budget, and your data integrity.
Protecting your SaaS isn't about being restrictive; it's about being smart. By implementing a multi-layered defense that starts with real-time email validation, you can reclaim your metrics.
Reducing registration fraud by 94% is an achievable goal that pays for itself in weeks. It is time to stop the giveaways and start driving real, measurable growth.
Begin by auditing your last 30 days of signups for disposable domains. That single step will show you exactly how much 'invisible churn' is currently hiding in your growth engine.