Is it Legal to Block Disposable Emails? GDPR and Privacy Compliance
Blocking disposable emails is a standard security practice, but it carries hidden legal risks under GDPR. This guide breaks down how to protect your platform without triggering 20 million Euro fines.
You are caught between a rock and a hard place. On one side, users demand absolute anonymity to avoid marketing spam, but on the other, your platform needs clean data to survive.
Allowing every burner address that hits your sign-up form is a recipe for database decay and trial abuse. It is a quiet killer of business metrics that many developers ignore until it is too late.
Between 2% and 10% of sign-ups on high-traffic consumer sites use disposable email addresses. These are not just privacy-conscious humans; they are often bots or users looking to recycle free trials indefinitely.
The legal question is simple: can you stop them? Privacy advocates argue that blocking infringes on data minimization rights, while businesses claim it is a matter of basic security.
The reality is that you can protect your platform without breaking the law. You just need to follow a specific compliance playbook that prioritizes transparency over secrecy.
The Bottom Line On Blocking Burner Emails
Blocking disposable email addresses is legal under GDPR and global privacy frameworks provided you meet transparency requirements. Most businesses rely on the Legitimate Interest clause to justify these security measures.
€20 Million maximum potential fine for severe GDPR violations.
- It is legal to block DEAs to prevent fraud and trial abuse.
- You must disclose email filtering in your Privacy Policy.
- Legitimate Interest must be documented internally.
- Tools must process data within compliant regions.
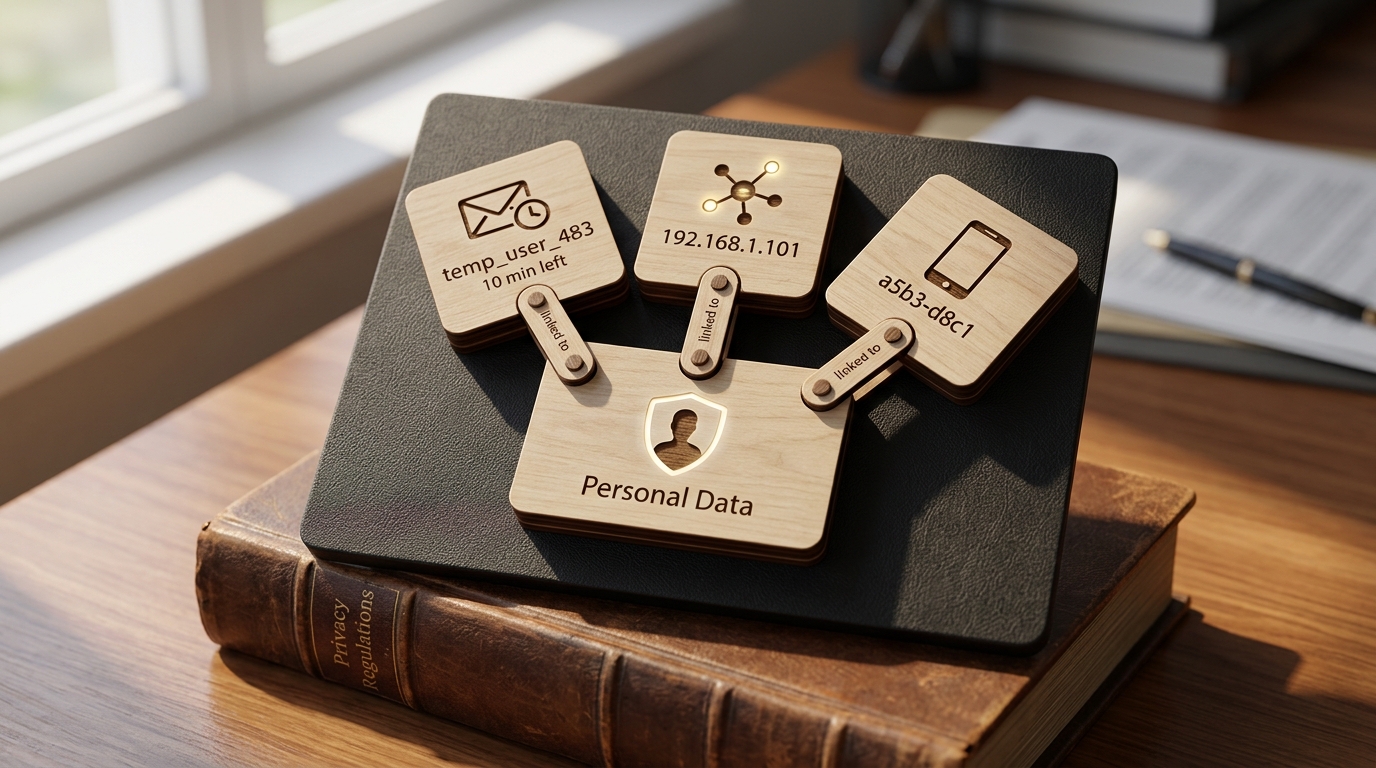
Why Temporary Emails Are Legally Considered Personal Data
A temporary email might feel anonymous, but under GDPR Article 4, it is still classified as personal data. This is because an email address relates to an "identifiable natural person" when combined with other metadata.
Even if the address lasts for only ten minutes, it can be linked to an IP address or a device ID. The ICO Guidance on Personal Data clarifies that any information that distinguishes one user from another falls under this umbrella.
Ephemeral data packages do not exempt you from privacy rules. You are still processing a unique identifier, which means your method of blocking must be grounded in a lawful basis.
If you use a third-party service to check these emails, that service becomes a data processor. This is why choosing a tool that respects data residency is critical for your compliance audit.
Before You Start Blocking: Compliance Essentials
Before you flip the switch on a blocking system, you need a paper trail. You cannot simply block domains without informing your users or documenting your reasoning.
- Updated Privacy Policy: Explicitly mention that you use email verification to maintain platform integrity.
- Legitimate Interest Assessment (LIA): Create an internal document explaining why blocking is necessary for fraud prevention.
- Compliant Verification Service: Select a tool like IsFakeMail that offers real-time detection without requiring authentication for standard API usage.
- EU Data Handling: Ensure your provider processes data in a way that respects regional privacy standards.
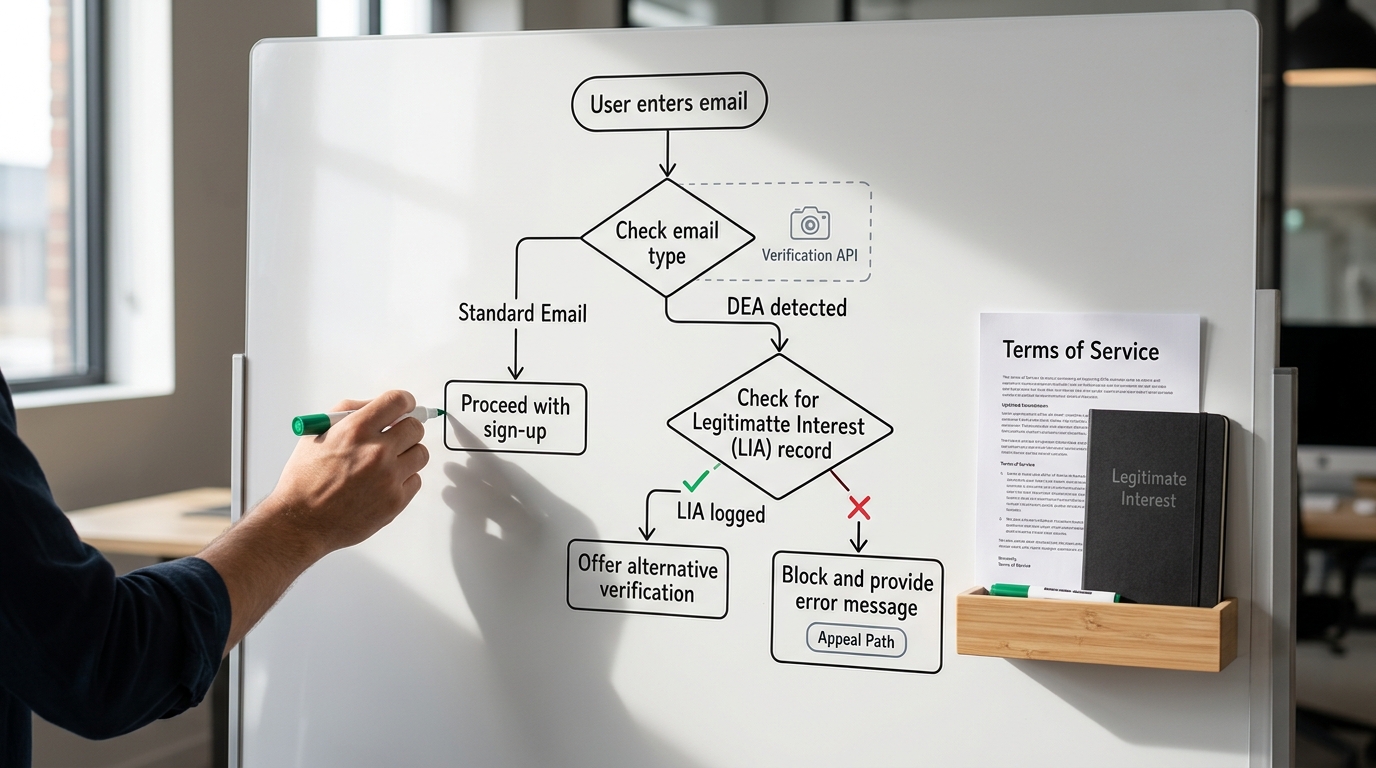
How To Legally Block Disposable Emails On Your Site
Start by auditing your current sign-up workflows to identify where fake accounts are causing the most damage. This might be in your free trial sign-ups or your discount code distributions.
Once you have identified the hotspots, you must update your Terms of Service. Transparency is the most common point of failure for websites that get flagged for non-compliance.
Here is a walkthrough that covers the key steps:
Integrate a real-time verification API at the point of entry. A service like IsFakeMail allows you to check domains or full addresses in under 50ms, ensuring your user experience remains fast.
- Identify high-risk entry points in your application.
- Update legal documents to cite Article 13 compliance regarding email filtering.
- Connect your sign-up form to a database of known disposable domains.
- Provide a clear error message to the user if their email is rejected.
- Establish an appeals process for users who believe they were blocked by mistake.
A developer at a mid-sized SaaS company recently implemented this to stop trial abuse. By blocking temporary domains at the registration gate, they saw a significant increase in lead quality and a drop in bot-driven server costs.
Navigating The Legitimate Interest Framework
The Legitimate Interest framework is your best friend when it comes to blocking burner emails. Recital 47 of the GDPR explicitly states that processing personal data for fraud prevention can be considered a legitimate interest.
Rule: Your interest in protecting your business model must not outweigh the user's fundamental rights and freedoms.
- If your goal is fraud prevention, blocking is generally permitted.
- If your goal is marketing growth, you need to be much more transparent about why you reject certain emails.
- If a user is from the EU or UK, ensure your verification tool is compliant with regional laws.
Transparency is the anchor for this entire legal strategy. As long as you tell users what you are doing and why, you are on solid ground.
When To Block vs. When To Allow
Not all blocking strategies carry the same legal weight. You must distinguish between protecting your infrastructure and simply being restrictive for the sake of marketing stats.
| Scenario | Risk Level | Best Practice |
|---|---|---|
| Fraud Prevention | Low | Use Legitimate Interest and update your Privacy Policy. |
| Trial Abuse | Low | Document the business impact in your LIA. |
| Marketing Lists | Medium | Clearly state that only permanent emails are accepted for newsletters. |
| Privacy Relays | High | Avoid blocking services like Apple's Hide My Email without a security reason. |
High-risk blocking occurs when you target privacy-focused relay services that are legitimate tools for user safety. Only block these if you can prove they are being used specifically for malicious activity.
Verify Your Compliance Status
Implementation is only half the battle. You need to verify that your system works as intended and does not create a secondary compliance liability.
- Error Messages: Confirm the sign-up form displays a clear reason why a submission was rejected.
- Data Storage: Verify that your verification service does not store plain-text emails in non-EU databases.
- Third-Party Filtering: Check that your Privacy Policy specifically mentions any third-party tools used for filtering.
- No-Auth API Usage: Use a service like IsFakeMail to avoid managing sensitive API keys for simple domain checks.
Regular audits of your blocklist help ensure you aren't accidentally rejecting legitimate university or corporate domains.
Frequently Asked Questions About DEA Legality
Is it legal to block all disposable email providers?
Yes, it is generally legal if you have a legitimate business reason, such as preventing fraud or protecting your infrastructure. You must ensure this is clearly stated in your Terms of Service to remain compliant with transparency requirements.
Does GDPR forbid blocking temporary emails?
GDPR does not forbid blocking, but it regulates how you process the data during the check. As long as you have a lawful basis like Legitimate Interest and you disclose the practice, you are compliant.
Should I block Apple's Hide My Email service?
It is generally recommended to allow Apple's relay service because it is a legitimate privacy tool for real users. Blocking it can be seen as an unnecessary restriction on user privacy unless you have specific evidence of abuse from those domains.
How do I handle false positives?
You should provide a clear error message and a way for users to contact support. This ensures that legitimate users who might be using a misclassified domain can still gain access to your service.
Balance Security With User Rights
Blocking disposable emails is a vital part of maintaining a healthy platform. When handled with transparency and the right tools, it is a perfectly legal way to protect your business from fraud.
Tip: Always use an API that updates its database in real-time to avoid blocking legitimate new domains.
Focus on clear communication with your users. By balancing security with privacy rights, you build a more resilient and trustworthy application.