5 Strategies for Preventing Multi-Account Fraud in Freemium SaaS
Freemium SaaS is a goldmine for 'Credit Bandits' and trial abusers. Learn how to identify and block multi-account fraud without killing your conversion rates.
One out of every three signups at your freemium SaaS is likely a ghost. They have no intention of ever paying for your product.
These users utilize disposable email addresses to bypass your paywalls and harvest your compute resources. Thirty-three percent of freemium signups are currently found to be using disposable domains.
When a 'Credit Bandit' creates 50 accounts to exploit your backend resources for free, your profit margins evaporate. You are essentially paying for their usage while they provide zero long-term value.
A free trial stops being a sales tool and becomes a liability the moment it becomes a loophole. This systematic abuse turns your growth engine into a massive financial drain.
The solution is not to kill the free trial entirely. It is to build a defense that distinguishes between a curious prospect and a professional abuser.
Bottom Line: How to Secure Your SaaS Funnel
Stopping multi-account fraud requires a layered defense that moves faster than the fraudsters. You cannot rely on a single check to protect your margins.
50% of SaaS fraud incidents begin with a fake signup using temporary credentials. By combining identity verification with hardware intelligence, you create a barrier that is too expensive for abusers to penetrate.
33% of signups use disposable domains
- Integrate real-time email validation.
- Deploy hardware-level device fingerprinting.
- Implement risk-based friction rules.
- Switch to value-based usage caps.
1. Block Disposable and 'Plus' Email Aliases
Disposable email addresses are the primary weapon for the serial trialist. These temporary inboxes allow users to create infinite accounts without ever using a real identity.
Real-time email verification blocks the most common entry point for multi-account fraud. By filtering domains at the point of registration, you stop the problem before it enters your database.
Many fraudsters also use the '+' character to create aliases of a single Gmail account. For example, user+1@gmail.com and user+2@gmail.com both go to the same inbox but appear as different accounts to your system.
Description
This strategy involves checking every signup against a list of known temporary email providers. It also identifies and normalizes email aliases to prevent users from registering multiple times with the same underlying inbox.
Tradeoff
Stricter rules might occasionally block a legitimate user who prefers a high degree of privacy. The cost of allowing thousands of fake signups usually outweighs the risk of one lost lead.
Implementation
You can use the IsFakeMail REST API to validate addresses during the signup flow. This service is free and identifies disposable domains and alias patterns without requiring complex authentication.
// Example of checking an email against the IsFakeMail API
async function validateEmail(email) {
const response = await fetch(`https://api.isfakemail.com/v1/validate/${email}`);
const data = await response.json();
return data.is_disposable; // Returns true if it's a throwaway domain
}
You should also consult the Clearout guide on trial abuse to understand how these aliases impact your long-term deliverability. It is critical to stop these signups before they pollute your marketing automation tools.
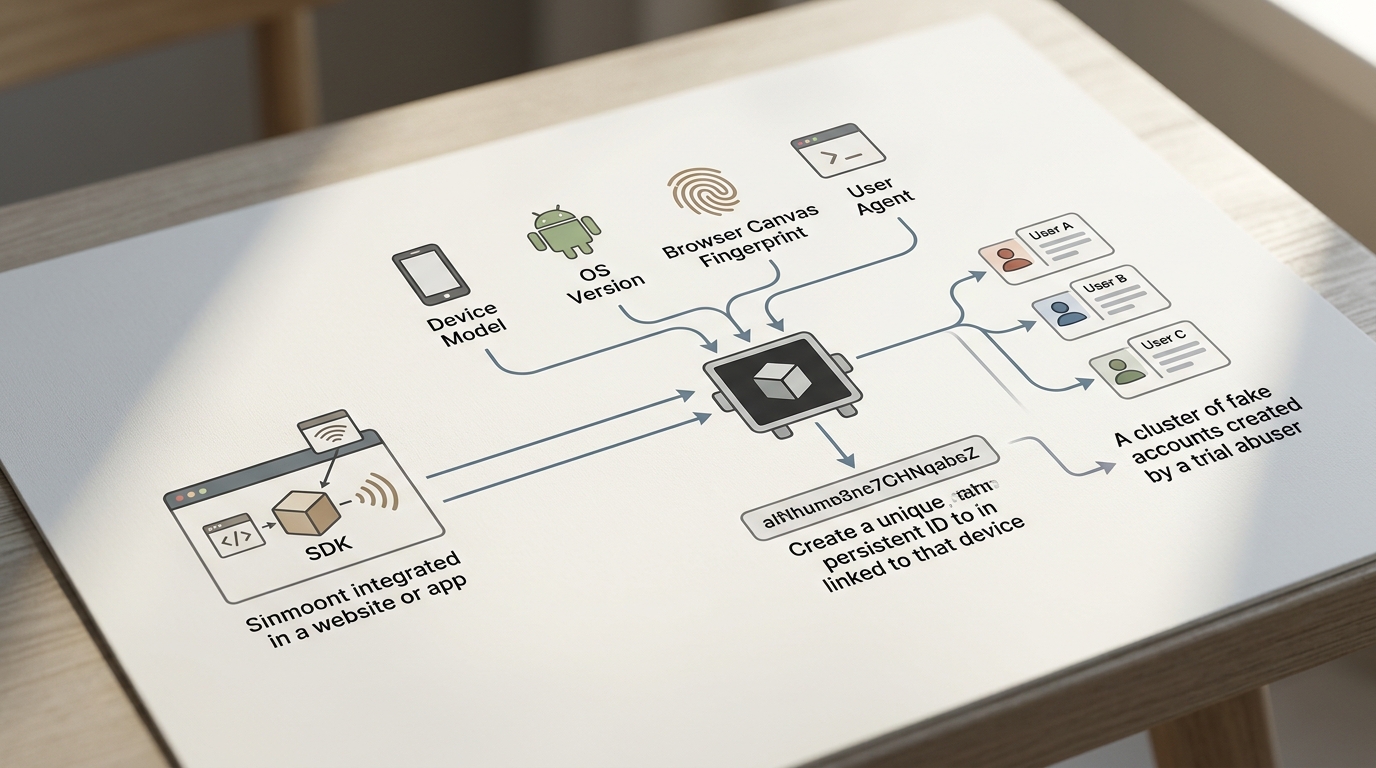
2. Deploy Invisible Device Fingerprinting
Standard tracking methods like cookies are useless against a savvy fraudster. They can simply open an incognito window or clear their cache to appear as a brand new visitor.
Device fingerprinting creates a persistent ID based on hardware and browser attributes. This unique identifier remains constant even if the user switches their IP address or clears their browser history.
Description
The system collects signals like screen resolution, installed fonts, and GPU rendering patterns. These data points are combined to form a digital fingerprint that identifies a specific device across multiple sessions.
Tradeoff
Collecting hardware signals can raise privacy concerns in certain jurisdictions. You must ensure your privacy policy accurately reflects your use of device intelligence to remain compliant.
Implementation
You can deploy the Fingerprint SDK to handle the heavy lifting of identification. It provides a stable ID that you can store alongside your user records to detect account clusters.
// Initializing a device intelligence SDK for multi-account detection
import FingerprintJS from '@fingerprintjs/fingerprintjs';
const fpPromise = FingerprintJS.load();
fpPromise
.then(fp => fp.get())
.then(result => {
const visitorId = result.visitorId;
console.log('Unique Device ID:', visitorId);
// Send visitorId to your backend to check for existing accounts
});
Linking multiple accounts to a single device ID allows you to trigger manual reviews automatically. This visibility is the only way to stop users from restarting trials on the same machine repeatedly.
3. Monitor Behavioral Biometrics and Velocity
Bots and professional fraudsters do not interact with software the way genuine humans do. They move with an efficiency that is statistically impossible for a person seeking to solve a genuine problem.
Behavioral biometrics track mouse movements and keystroke cadence to identify non-human behavior. If a user navigates through your entire onboarding flow in under three seconds, they are likely an automated script.
Description
This layer of defense looks at how a user moves through your interface. It monitors velocity checks, which track the speed and volume of signups from specific IP ranges or network providers.
Tradeoff
This requires sophisticated data processing and can be difficult to implement correctly without specialized third-party tools. The complexity of behavior analysis often demands a dedicated fraud engine.
Implementation
Monitor the time spent on each signup page and flag users who complete forms faster than humanly possible. You should also check for a lack of mouse movement or unnatural scrolling patterns.
Example
Imagine a user who fills out a 5-field signup form in 200 milliseconds. A legitimate human requires time to type and move their cursor, but a script injects the data instantly. By flagging this behavior, you can block the account before it ever gains access to your compute resources.
4. Implement Risk-Based Step-Up Friction
Friction is a double-edged sword for SaaS companies. Too much friction kills your conversion rate, but too little friction invites every abuser on the internet to your platform.
Risk-based friction only challenges suspicious users while keeping the path clear for honest customers. This dynamic approach ensures that high-quality leads never see a CAPTCHA or a credit card requirement.
Description
You assign a fraud score to every visitor based on their email, IP, and device data. Users with a low score proceed instantly, while those with high scores must complete extra verification steps like SMS or ID checks.
Tradeoff
Building the logic gates for different friction levels adds complexity to your authentication flow. Maintaining a balanced risk threshold requires constant monitoring and adjustment.
Implementation
Use an intelligence platform to calculate these scores in the background during the signup process. If a score exceeds your threshold, your frontend should dynamically render a verification challenge.
- If the user has a high-risk IP, require SMS verification.
- If the user uses a disposable email, block the signup entirely.
- If the hardware ID is linked to existing accounts, require a credit card for the trial.
- If the behavioral signals suggest a bot, present a silent honeypot challenge.
Using silent honeypots for bots is more effective than intrusive CAPTCHAs. This allows you to protect your platform without annoying your real customers who are trying to explore the product.
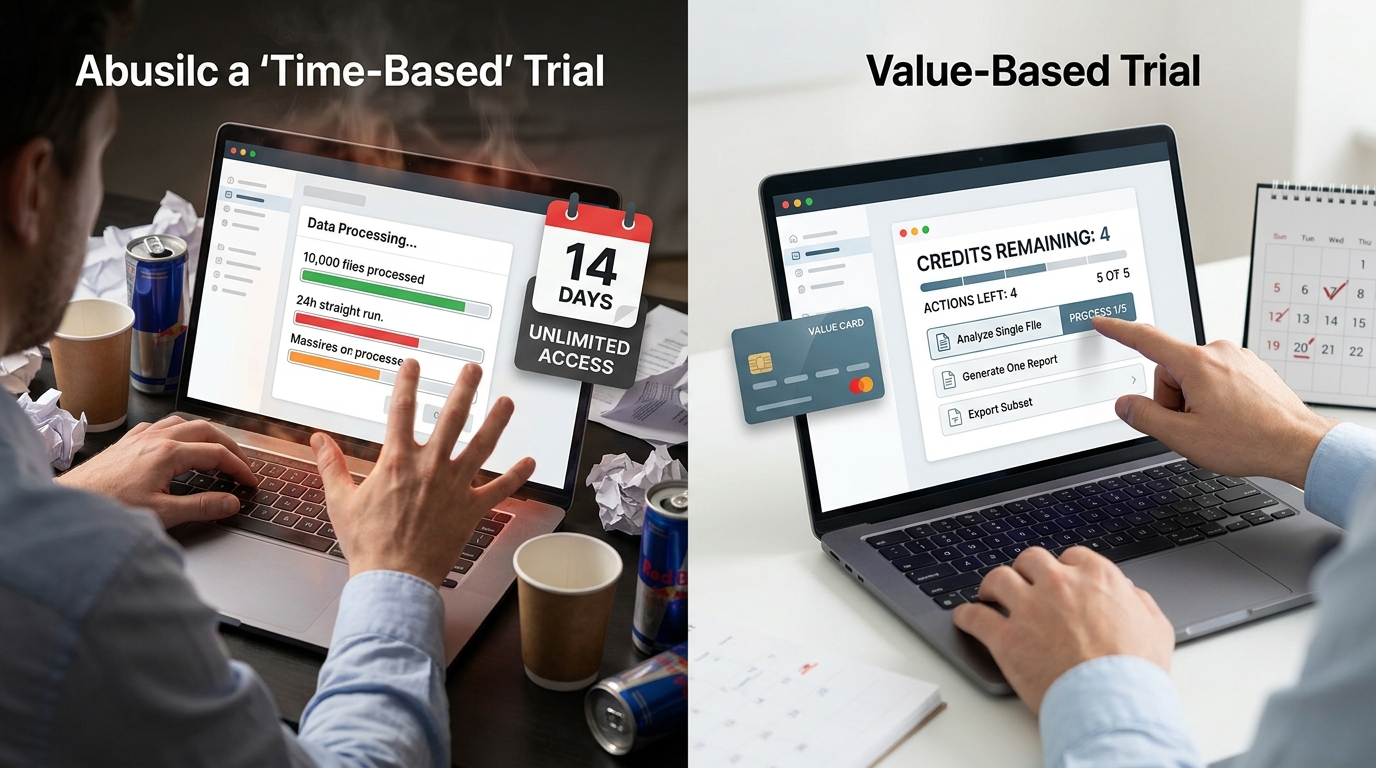
5. Pivot to Value-Based Usage Caps
Time-based trials are inherently vulnerable to harvesting. If you give a user 14 days of unlimited access, they will find a way to extract as much value as possible in those two weeks.
Value-based usage caps limit specific actions rather than the length of the trial. This ensures that your costs remain predictable and prevents users from burning through expensive compute resources.
Description
Instead of a time window, you provide a set number of credits or actions. Once the user reaches a specific limit of AI generations or document exports, the trial ends unless they upgrade to a paid plan.
Tradeoff
This may feel more restrictive to some exploratory users who want to test every corner of your platform without constraints. The benefit is that your resource costs are capped per user.
Implementation
Move your trial logic to a credit-based ledger in your database. Every time a protected action is performed, decrement the user balance and block further requests when the balance reaches zero.
Rule: Always monitor trial usage density to identify fraudulent patterns. Fraudsters often exhaust their entire credit limit in less than 24 hours to maximize their ROI before detection.
Transitioning to value-based limits protects your margins from high-cost compute activities. It changes the trial from a time-limited gift into a direct sample of the value your software provides.
Choosing the Right Defense Layer
| Strategy | Implementation Effort | Fraud Effectiveness | UX Friction |
|---|---|---|---|
| Email Aliases | Low | Moderate | Low |
| Device Fingerprinting | Moderate | High | None |
| Behavioral Biometrics | High | High | None |
| Risk-Based Friction | Moderate | High | Dynamic |
| Value-Based Caps | Moderate | Moderate | Moderate |
Each defense layer serves a different purpose in your security stack. Email verification provides the first line of defense at a very low cost. Device fingerprinting then ensures that users cannot simply rotate identities to start over. For high-cost services, risk-based friction and usage caps are the final barriers that protect your infrastructure from being drained by automated scripts.
How to Implement Your Anti-Fraud Roadmap
Building an anti-fraud roadmap requires a systematic approach to avoid breaking your user experience. Start with visibility before you move to blocking.
Audit your existing signups for IP and device clusters to identify the scale of your current problem. This data will help you set the correct thresholds for your risk scoring.
- Audit existing logs for multiple accounts sharing a single device ID or IP.
- Integrate an email validation API at your signup endpoint to block temporary domains.
- Deploy a device intelligence SDK to track users across incognito sessions.
- Establish velocity checks to flag bursts of activity from specific networks.
- Monitor the conversion rate from trial to paid to verify the efficacy of your defenses.
Check your trial usage density to see if users are exhausting credits in short bursts. Fraudulent accounts rarely convert to paid plans, making them easy to spot in your cohort analysis. By following these steps, you can secure your funnel without impacting your growth metrics.
Secure Growth Requires Smart Protection
Fraud prevention is a necessary part of scaling any freemium software. By implementing these strategies, you protect your margins and ensure that your resources go to legitimate potential customers.
Can I just block all Gmail users?
Blocking all free email providers is generally a mistake because it alienates legitimate personal-use customers. It is better to use an API to block only disposable domains and handle alias normalization.
How does device fingerprinting handle VPNs?
Device fingerprinting looks at hardware and browser signals rather than network data. Even if a user changes their IP with a VPN, their hardware signature remains the same.
Is SMS verification effective?
SMS verification is highly effective against low-level abusers but can be bypassed by professional fraud rings using SIM farms. Use it as a step-up challenge for medium-risk users only.
How do I know if my fraud rules are too strict?
Monitor your signup-to-trial conversion rate closely after implementing new rules. If your conversion rate drops significantly while your fraud metrics stay the same, you may be blocking real customers.
Stop letting trial abusers burn your budget. Focus on building a secure platform that rewards genuine users.